Building Over-The-Horizon Defensive Capabilities
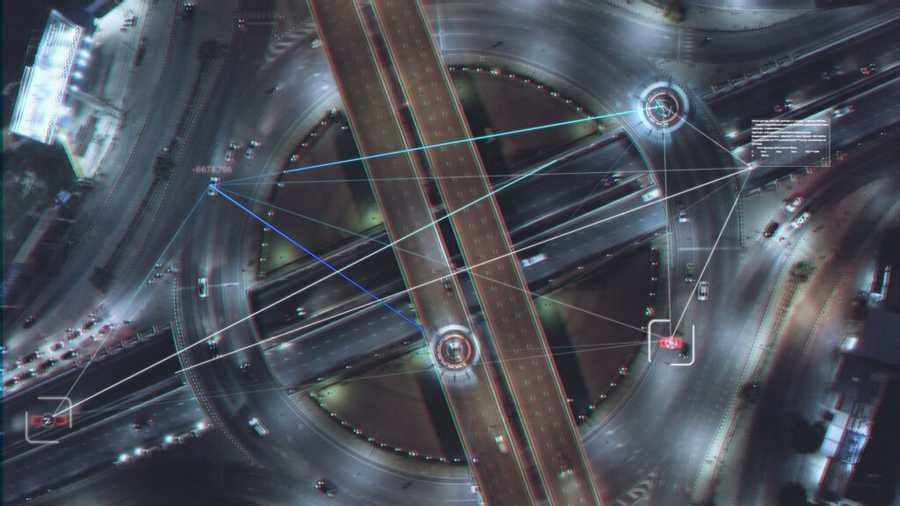
Mitigating the cybersecurity risks of on-demand access to ubiquitous data requires four cybersecurity capabilities: zero-trust capabilities, behavioural analytics, elastic log monitoring, and homomorphic encryption.
8
30 reads
CURATED FROM
IDEAS CURATED BY
The idea is part of this collection:
Learn more about cybersecurity with this collection
Understanding machine learning models
Improving data analysis and decision-making
How Google uses logic in machine learning
Related collections
Similar ideas to Building Over-The-Horizon Defensive Capabilities
Building ethical AI
Companies are leveraging data and artificial intelligence to create scalable solutions — but they’re also scaling their reputational, regulatory, and legal risks. For instance, Los Angeles...
The solution comes in two phases
This revolutionary tech takes “root source” quantum keys that are stored in data centres and uses them as an ingredient in a novel process whereby two or more end point devices create symmetric encryption keys locally. This process is both zero trust and computationally secure.
Today, the ...
The future is data analysis
Our digital economy has evolved beyond the point where data collection alone can facilitate success.
Now, getting ahead requires collecting and evaluating data to gather crucial insights on market demand, running lean and generating consistent returns.
Read & Learn
20x Faster
without
deepstash
with
deepstash
with
deepstash
Personalized microlearning
—
100+ Learning Journeys
—
Access to 200,000+ ideas
—
Access to the mobile app
—
Unlimited idea saving
—
—
Unlimited history
—
—
Unlimited listening to ideas
—
—
Downloading & offline access
—
—
Supercharge your mind with one idea per day
Enter your email and spend 1 minute every day to learn something new.
I agree to receive email updates