Encrypted Storage
- VeraCrypt: A free and open-source disk encryption software that allows you to create encrypted volumes on your device.
- Cryptomator: Encrypts files before uploading them to cloud storage, ensuring that even if the cloud provider is compromised, your files remain secure.
358
1.04K reads
CURATED FROM
IDEAS CURATED BY
This guide is designed to help you maintain the highest level of operational security (OpSec), prioritizing freedom, privacy, and zero logs. By following these practices, you’ll reduce your digital footprint and protect your personal information from being tracked or logged.
“
Similar ideas to Encrypted Storage
The solution comes in two phases
This revolutionary tech takes “root source” quantum keys that are stored in data centres and uses them as an ingredient in a novel process whereby two or more end point devices create symmetric encryption keys locally. This process is both zero trust and computationally secure.
Today, the ...
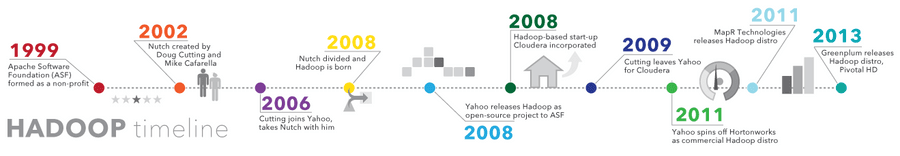
Big data Hadoop
- Ability to store and process huge amounts of any kind of data, quickly. With data volumes and varieties constantly increasing, especially from social media and the Internet of Things (IoT) , th...
Read & Learn
20x Faster
without
deepstash
with
deepstash
with
deepstash
Personalized microlearning
—
100+ Learning Journeys
—
Access to 200,000+ ideas
—
Access to the mobile app
—
Unlimited idea saving
—
—
Unlimited history
—
—
Unlimited listening to ideas
—
—
Downloading & offline access
—
—
Supercharge your mind with one idea per day
Enter your email and spend 1 minute every day to learn something new.
I agree to receive email updates