3. How do zero-day attacks work?
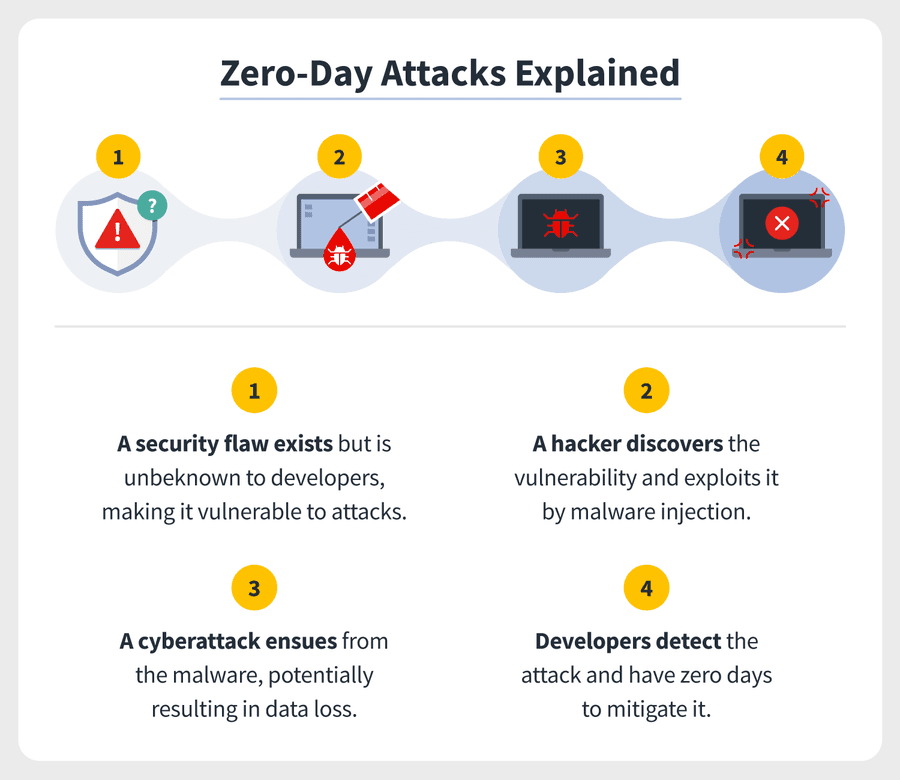
Zero-day attacks begin with zero-day vulnerabilities, meaning flaws or holes in security software. These can result from improper computer or security configurations or programming errors by developers themselves. The whole notion of a zero-day attack is that cyber attackers exploit these vulnerabilities without developers knowing. Cyberattackers might write — or purchase from the dark web — exploit codes to spot these vulnerabilities. When they do, it’s akin to a welcome mat for a zero-day attack.
65
675 reads
CURATED FROM
Zero-day vulnerability: What it is, and how it works
unboxingspace21.blogspot.com
15 ideas
·7.61K reads
IDEAS CURATED BY
Hi, Readers we are Unboxing Space here we do all kind of Tech videos, Unboxing, Review, Tips & Tricks, Information & so many interesting things. To watch our videos you can SUBSCRIBE to our channel & Blog so you don’t Miss any informative thing. by IGDM
Nowadays it is important to be aware of this kind of thing, So just Trying to add Value...
“
The idea is part of this collection:
Learn more about cybersecurity with this collection
How to build trust in a virtual environment
How to manage remote teams effectively
How to assess candidates remotely
Related collections
Read & Learn
20x Faster
without
deepstash
with
deepstash
with
deepstash
Personalized microlearning
—
100+ Learning Journeys
—
Access to 200,000+ ideas
—
Access to the mobile app
—
Unlimited idea saving
—
—
Unlimited history
—
—
Unlimited listening to ideas
—
—
Downloading & offline access
—
—
Supercharge your mind with one idea per day
Enter your email and spend 1 minute every day to learn something new.
I agree to receive email updates